#cisco
#cisco = #ProprietarySoftware #backdoors ... never made to be truly secure https://us-cert.cisa.gov/ncas/current-activity/2022/02/24/cisco-releases-security-updates-multiple-products
#msa : #cisco has bug doors, but please use Cisco https://hackaday.com/2022/02/18/this-week-in-security-chrome-0-daycassandra-and-a-cisco-poc/
NSA won't tell you to discard Cisco altogether as #NSA controls #Cisco https://us-cert.cisa.gov/ncas/current-activity/2022/02/17/nsa-best-practices-selecting-cisco-password-types
#cisco #proprietarySofrware "A remote attacker could exploit this vulnerability to cause a denial-of-service condition." https://us-cert.cisa.gov/ncas/current-activity/2022/02/17/cisco-releases-security-updates-email-security-appliance
#cisco still renowned for its bug doors https://www.theregister.com/2022/02/04/cisco_smb_routers_critical_vulnerabilities/
#cisco junk (where #backdoors are likely the actual goal): "A remote attacker could exploit some of these vulnerabilities to take control of an affected system." https://www.cisa.gov/uscert/ncas/current-activity/2022/02/03/cisco-releases-security-updates-rv-series-routers
#Marktführer #Cisco #Myass
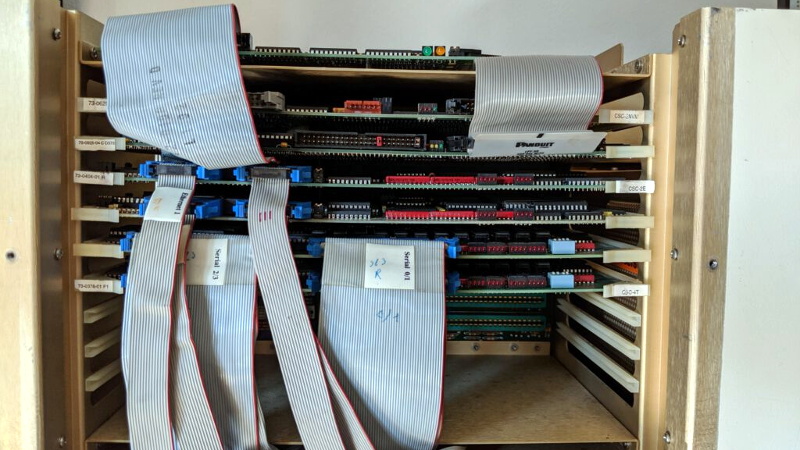
Ein Catalyst 9000:
~$ ssh -l admin x.x.x.x
Unable to negotiate with x.x.x.x port 22: no matching key exchange method found. Their offer: diffie-hellman-group-exchange-sha1,diffie-hellman-group14-sha1
~$
SHA-1, ist klar.
#cisco "An attacker could exploit some of these vulnerabilities to take control of an affected system" https://us-cert.cisa.gov/ncas/current-activity/2022/01/20/cisco-releases-security-updates-multiple-products
~$ lynx -dump https://github.com/NCSC-NL/log4shell/tree/main/software | grep tools.cisco.com | wc -l
156
~$
[l] Benutzt hier jemand Cisco-Geräte?
Nein, nein, keine Sorge. Diesmal waren es keine hartkodierten Backdoor-Passwörter. Diesmal waren es "unintentional debugging credentials". Das ist was GANZ anderes!!1!
Diesmal war es keine Absicht!1!!
So glaubt uns doch!
Oh, warte, das war noch nicht alles!
The other critical hole is CVE-2021-40113, which can be exploited by an unauthenticated remote attacker to perform a command injection attack on the equipment's web-based management portal, thanks to insufficient validation of user-supplied input.
Einmal mit Profis!
"A successful exploit could allow the attacker to execute arbitrary commands on an affected device as the root user."
Was macht die Security-Abteilung bei Cisco eigentlich beruflich?
Haha. #cisco #proprietarySoftware (made for spying anyway) "vulnerabilities in multiple Cisco products. A remote attacker could exploit some of these vulnerabilities to take control of an affected system" https://us-cert.cisa.gov/ncas/current-activity/2021/10/28/cisco-releases-security-updates-multiple-products
#ibm #cisco #microsoft et al: you cannot say slavery because slavery is what we do for profit and we hate it when people point out that we're gaining from slavery
MoUs for algorithms and data for profit: 4 new MoUs signed between the Ministry of #Agriculture and private corporations, including Jio and #Cisco. ⚓ https://internetfreedom.in/algorithms-in-mous-and-data-for-profit-4-new-mous-signed-between-the-ministry-of-agriculture-and-private-corporations-including-jio-and-cisco/ ䷉ #internetfreedom #india #slavery
Nobody does #backdoors as well as #juniper and #cisco (or call them #bugdoors if you like; same effect) https://us-cert.cisa.gov/ncas/current-activity/2021/10/07/cisco-releases-security-updates-multiple-products
#cisco was never designing for #security but for back door access or so-called 'legal intercepts' https://us-cert.cisa.gov/ncas/current-activity/2021/09/23/cisco-releases-security-updates-multiple-products
#cisco #fraud https://www.theregister.com/2021/08/31/former_cisco_exec_jailed/ why don't they jail people from #microsoft too? Too many government officials bribed already? http://techrights.org/2021/03/17/epoleaks-report-march-2021-part-12/