.webp)
PIKABOT is a polymorphic malware that constantly modifies its code, making it hard to recognize and easily bypasses the Endpoint Detection and Response (EDR) systems.
Obfuscation, encryption, and anti-analysis techniques help the object avoid these traditional security measures.
PIKABOT is able to avoid signature-based detection by dynamically changing its structure, which makes it harder for EDR solutions to keep up with their ever-changing behaviors.
Cybersecurity researchers at Elastic Security Labs recently discovered new and upgraded PIKABOT campaigns on February 8th.
A popular loader used by malicious actors to disseminate extra payloads is called PIKABOT.
Technical Analysis
Elastic Security Labs detected a fresh instance of PIKABOT with the updated loader, new unpacking method, and heavy obfuscation for strings decryption as well as other obfuscation changes.
The update is an indication that a new code base has been laid down for future improvements.
However, these changes are expected to break signatures and previous tools like the previous versions.
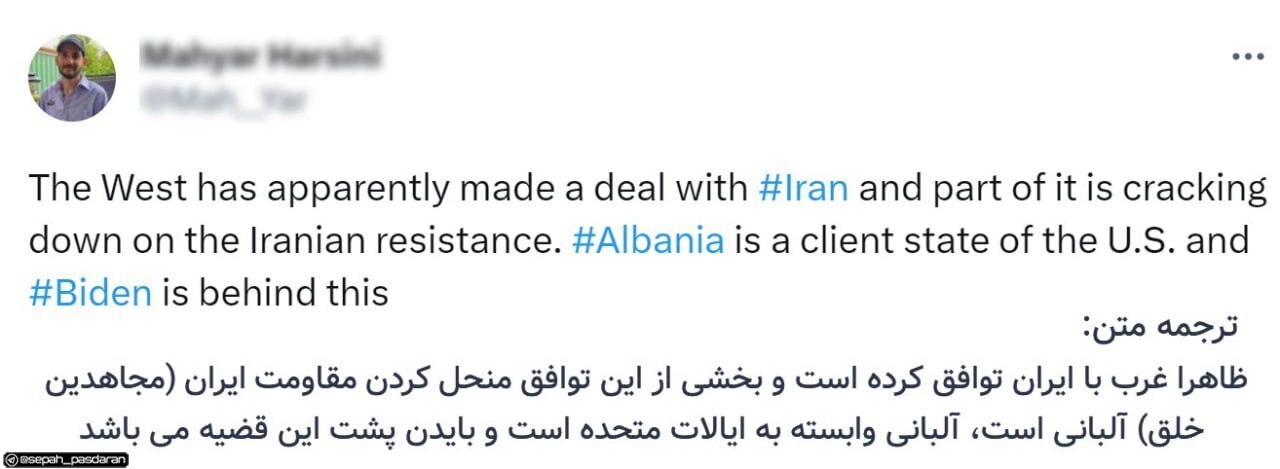
.webp) PIKABOT execution flow (Source – Elastic)
PIKABOT execution flow (Source – Elastic)
PIKABOT has been quiet during the New Year but resurfaced in February, with a campaign launched on Feb 8.
ZIP archives in emails contained hyperlinks to download obfuscated Javascript.
The attacker altered grepWinNP3.exe, which is a legitimate tool, to appear real.
The call stack analysis traced back malicious code entering their Detonate sandbox and Elastic Defend’s call stack.
Executions begin before offset 0x81aa7 and jump towards memory allocation at offset 0x25d84 as indicated by this last part of the previous sentence.
There were no normal calls for process creation; instead, there were unbacked memory syscalls via shellcode evading EDR products and bypassing user-mode hooks on WOW64 modules.
In a hard-coded address for PIKABOT loader execution at offset 0x81aa7, researchers found. JMP instructions are used after each assembly line in the code to make analysis difficult because of heavy obfuscation.
This loader uses custom decryption by means of bitwise operations to recover its payload from the .text section.
However, this can lead to any PE file not being written into a disk and executed in memory.
By doing this, on the host system, the stealth is improved by reducing the digital footprint.
The PIKABOT core is initialized by the stage 2 loader using code and string obfuscation, NTDLL Zw APIs, and advanced anti-debugging.
Moreover, the PIKABOT core makes direct system calls, allowing it to bypass EDR user-land hooking and debugging.
Besides, malware utilizes ZwQuerySystemInformation, ZwQueryInformationProcess, PEB inspection, GetThreadContext methods, and many others as techniques that are undetected by forensic and debugging tools.
The current version of PIKABOT core functions similarly with its previous releases.
However, there are some differences, such as a new obfuscation style, different string decryption processes, use of plain text configuration, and network communication changes (RC4 instead of AES).
This binary is relatively less obfuscated but still remains familiar. The remaining in-line RC4 functions utilize legitimate strings as keys.
Obfuscation is done through junk code insertion to confuse an analyst. While the command execution, discovery, and process injection form part of core functionality.
The Twitter user reecDeep, who specializes in malware analysis, noticed that Pikabot malware is being distributed by TA577 through HTML files.
⚠️TA577 starts spreading
[
#Pikabot
](https://twitter.com/hashtag/Pikabot?src=hash&ref_src=twsrc%5Etfw)
[
#malware
](https://twitter.com/hashtag/malware?src=hash&ref_src=twsrc%5Etfw)
eml>.zip>.html(link)
html files with 0 detections on Virustotal and decoy latin words
🔥staging ip:
204.44.125.68
103.124.104.76
103.124.104.22
66.63.188.19
104.129.20.167
[
#infosecurity
](https://twitter.com/hashtag/infosecurity?src=hash&ref_src=twsrc%5Etfw)
[
#CyberAttack
](https://twitter.com/hashtag/CyberAttack?src=hash&ref_src=twsrc%5Etfw)
[
pic.twitter.com/0VXEGlqCjA
](https://t.co/0VXEGlqCjA)
— reecDeep (@reecdeep)
[
February 26, 2024
](https://twitter.com/reecdeep/status/1762081212124827948?ref_src=twsrc%5Etfw)
Surprisingly, these files have not been detected by any of the antivirus programs on VirusTotal.
You can block malware, including Trojans, ransomware, spyware, rootkits, worms, and zero-day exploits, with Perimeter81 malware protection. All are extremely harmful, can wreak havoc, and damage your network.
*Stay updated on Cybersecurity news, Whitepapers, and Infographics. Follow us on LinkedIn & Twitter.*
The post Heavily Obfuscated PIKABOT Evades EDR Protection appeared first on GBHackers on Security | #1 Globally Trusted Cyber Security News Platform.
posted by pod_feeder



 Countries affected by RA World ransomware based on the group’s leak site
Countries affected by RA World ransomware based on the group’s leak site The RA World attack chain
The RA World attack chain Stage1.exe checks if the conditions are met before proceeding
Stage1.exe checks if the conditions are met before proceeding The RA World ransom note
The RA World ransom note.webp)